Summary / TLDR
- End-to-end Encryption is currently available to all users who opt in. Opt in at app.truple.io/account.
- End-to-end Encryption is a huge step forward in keeping your data private, and puts you in control of your data
- Truple is the first accountability app to offer End-to-end Encryption
End-to-end Encryption
Every company claims they care about your privacy. We really do. What you do on the internet should be kept private from the world, but not necessarily your loved ones. With this in mind, we are proud to announce that Truple is the first accountability app to offer end-to-end encryption.
Support for end-to-end encryption (e2ee) is in an early release state [publicly released]. Review the update log below to learn more about the current status. While the software is being stabilized end-to-end encryption will remain optional. Once stabilized it will become required.
Updates:
- 7/8/2020 - Initial release of End-to-end Encryption for Android, Windows, MacOS, and Linux. You must opt in from the Accounts page (app.truple.io/account), and access is limited to testers. Email support@truple.io if you’d like your account to be marked as a tester.
- 7/9/2020 - Chrome OS Extension supporting End-to-end Encryption submitted to Google for review.
- 7/15/2020 - E2EE released for everyone, still optional.
- 1/22/2021 - E2EE publicly released, still optional, but strongly recommended and part of the setup guide.
For more information, please review the FAQ below. Any remaining questions can be emailed to support@truple.io.
Get Started
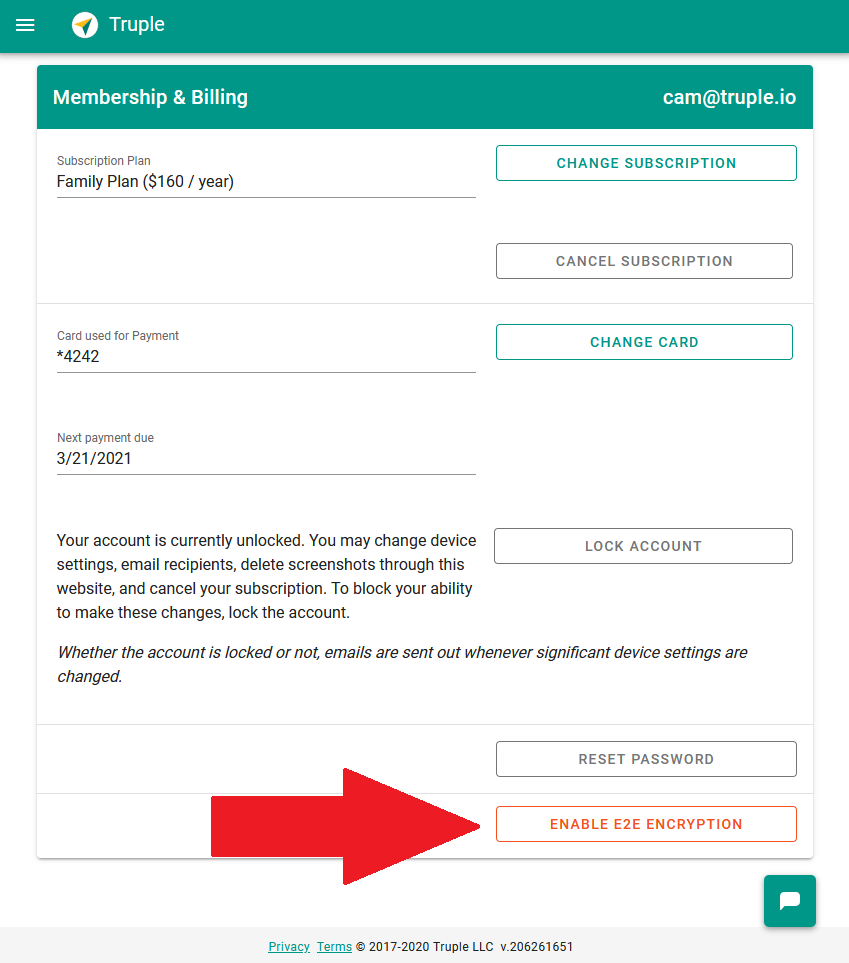
End-to-end encryption can be enabled for your account by visiting the accounts page.
End-to-end Encryption Frequently Asked Questions
What is End-to-end Encryption?
Pretend you want to open a safety deposit box at a bank. The bank offers two types of safety deposit boxes.
- One box requires a single key to open. The key is held by the bank, stored in a safe, and only pulled out when requested by a bank customer to open their box.
- The second type of safety deposit box requires two keys. It requires the same bank key, but it now also requires an additional key that stays with you.
These two different styles of safety deposit boxes describe, in a simplified way, the difference between common encryption and end-to-end encryption. Truple’s End-to-end Encryption (E2EE) requires two keys to decrypt the data. One key is held by Truple and another by you and your report recipients. This second key means that even if Truple were to get hacked and the hacker stole your data files from Truple’s database and stole Truple’s key, the hacker would also need to obtain your key (recovery passcode or private key) before they could decrypt the end-to-end encrypted data.
What benefits are there to using E2EE?
End-to-end encryption puts you in control of your data and prevents others from being able to read your data unless they obtain your E2EE recovery passcode or an unencrypted form of the private key that stays on you and your report recipient’s devices. Your passcode and unencrypted private key are never sent to Truple’s servers.
What drawbacks are there to using E2EE?
You will have to share your E2EE recovery passcode with your report recipients, enabling them to decrypt the data. You and your report recipients will have to provide this passcode at least one time on each device / browser you use to decrypt the data.
What data is encrypted end-to-end?
Screenshots and data describing websites visited and apps used are encrypted end-to-end. Timestamps are only encrypted using common encryption to enable us to provide accurate time based queries and to scale our services. Tamper alerts and queries sent to Truple's contextual data rating service* are only encrypted with common encryption, however this data isn’t persisted beyond temporary, short lived log files on Truple’s servers. We will continue to look for ways to provide E2EE for this data as well.
* On 10/26/21, we upgraded the contextual rating engine. See this blog post for more details.
How does Truple’s E2EE recovery passcode work?
The E2EE recovery passcode is a shared password between you and your report recipient. Think of it sort of like a Wifi password. Anyone who wants to be able to decrypt your data will need that passcode.
Technically speaking, a strong key is derived from your passcode using elliptic curve BLS12-381. This derived key is then used to encrypt your account’s private key before backing it up online. This allows you to access your encrypted data from new devices that don’t have your private key by simply by entering your E2EE recovery passcode.
I thought Truple already encrypted my data?
We do! End-to-end encryption is different from normal encryption. End-to-end encryption adds an additional layer of protection that you control around your data.
How do I know if my data is using e2ee?
End-to-end encrypted data is identified by having a key symbol 🔑 next to it. When that key is present, the data is end-to-end encrypted.
Why is a recovery passcode required?
End-to-end encryption requires that a special file, called a private key, remains on your device. The only way to decrypt information is with that key. End-to-end encryption is achieved when that key never leaves your device in a way that anyone else could use it. The recovery passcode allows Truple to make a backup of the private key in an encrypted format that only people who know your recovery passcode can decrypt.
Never miss a blog post. Subscribe now!